PCI compliance security training makes it easy to educate your employees on the PCI Data Security Standard (DSS), proper computer security and data security behavior.
Cybercrime is the fastest growing crime in the world. Our personal and business accounts are being attacked daily. These PCI Compliance Level I and Level II security training courses are designed to help businesses and organizations not only comply with the PCI DSS employee training standards, but when combined with CFISA’s Cyber Security Awareness Training, it empowers your employees to protect your organization and customer data.
If you accept, manage, or transmit Credit Cards and the personal information contained in the card, you need to train your employees upon hire and annually to be PCI DSS compliant.
PCI DSS Security Training Sample Lesson & Quiz
Here’s a two minute clip of our “PCI DSS Employee Security Training” lesson.
This is one of 15 lessons included in the PCI Compliance Level II Course. 111 total minutes of PCI DSS security training for your employees!
Start Training Today
- $12.95 per employee per month — only pay for employees that login and train.
- One-time $9.95 setup fee.
- Billing occurs at month-end based on employees that trained during the month.
- Includes access to all Security Awareness, HIPAA and PCI courses.
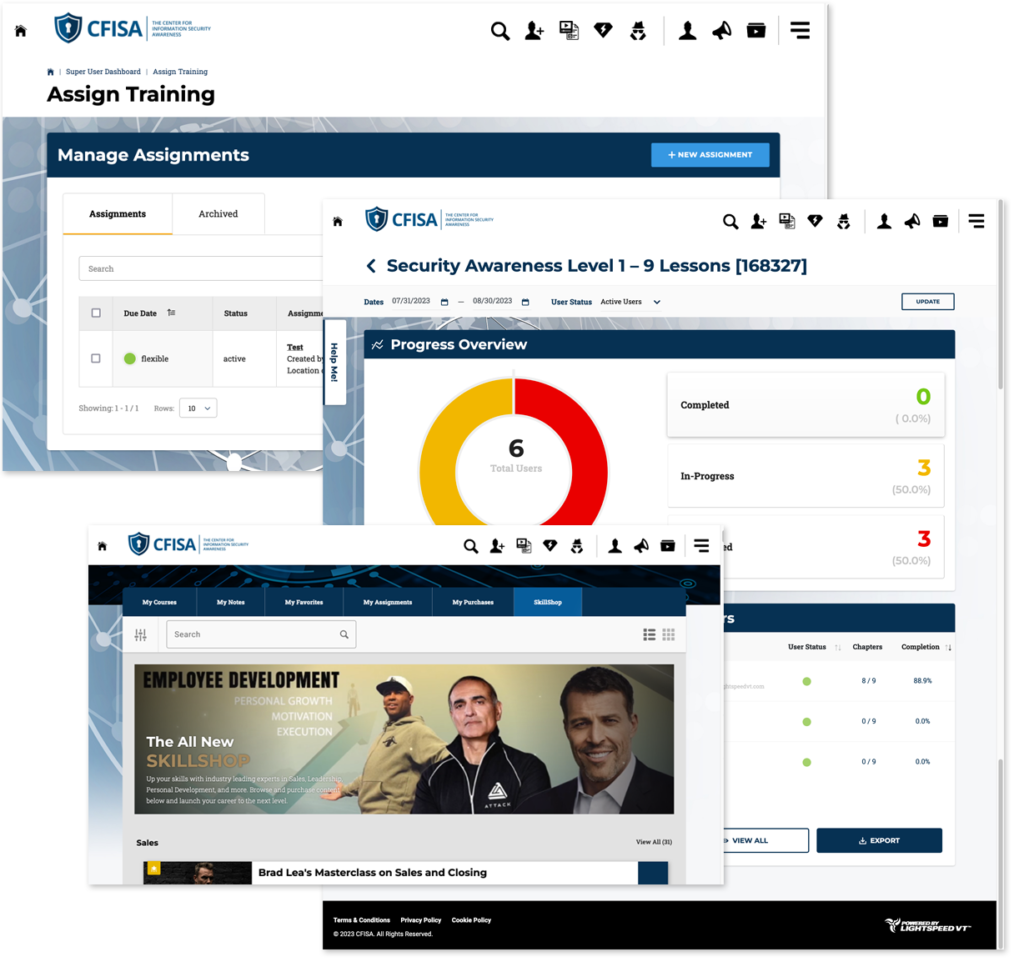
- Click ‘Continue’ at right, complete checkout and enroll employees, individually or in bulk.
- Employees simply log in and complete the course.
- Managers have access to progress and completion reports and certificates of completion.
All CFISA Courses Now Included
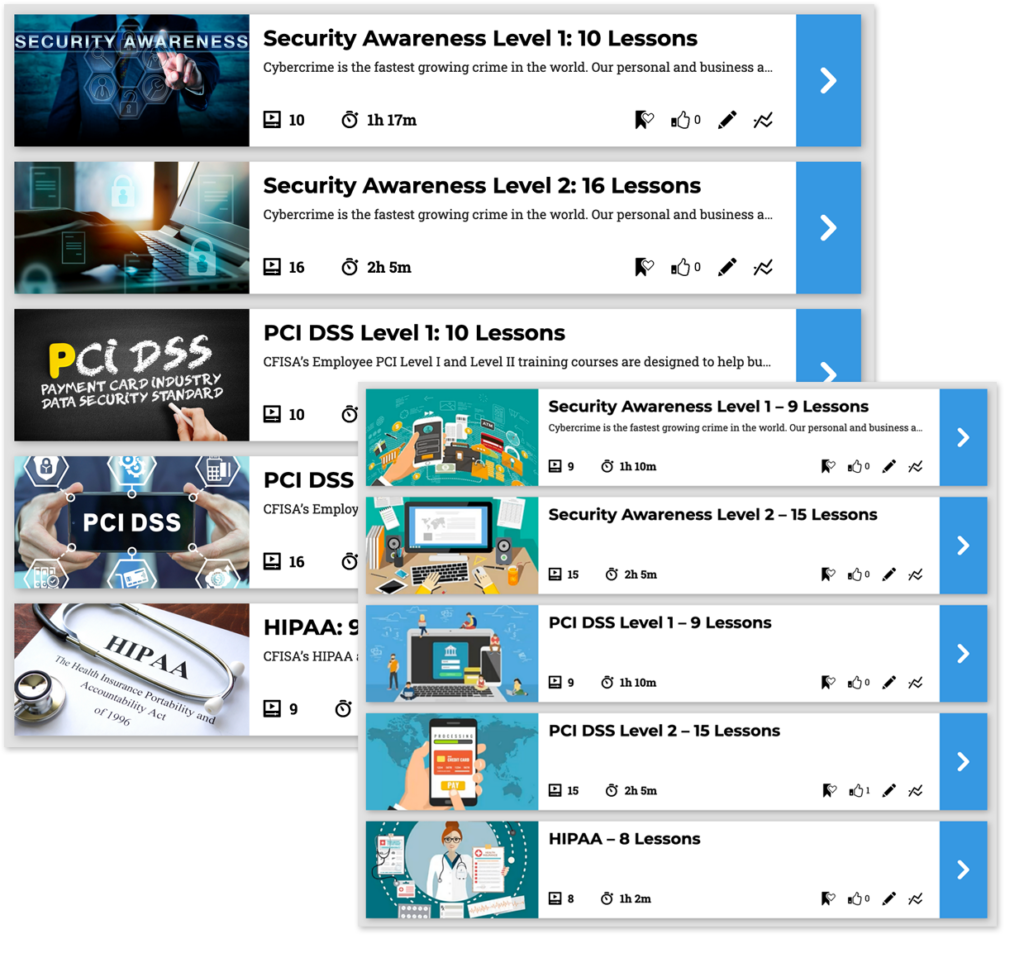 CFISA monthly subscriptions now include all of the NEW Security Awareness Courses and first generation courses for a single monthly price. Save time and money by enrolling employees in any or all of the courses below for no additional fee!
CFISA monthly subscriptions now include all of the NEW Security Awareness Courses and first generation courses for a single monthly price. Save time and money by enrolling employees in any or all of the courses below for no additional fee!
- Security Awareness Level I
- Security Awareness Level II * (Course certified by the State of Texas)
- PCI Compliance Level I
- PCI Compliance Level II
- HIPAA Compliance
PCI Compliance Course Lessons
| Level I | Level II | |
|---|---|---|
| PCI-DSS Overview – 5:55 min | X | X |
| The Impact of Cybercrime and Identity Fraud – 8:00 min | X | |
| Today’s Threats – 7:39 min | X | |
| How Behavior is Exploited by Cybercriminals – 9:27 min | X | |
| Strong Passwords Increase Security – 9:36 min | X | X |
| Understanding and Recognizing Social Engineering – 4:26 min | X | X |
| Phishing and Email Best Practices – 6:35 min | X | X |
| Protecting Against Viruses, Spyware and Spam – 6:30 min | X | X |
| Protecting Your Personal Workspace – 5:27 min | X | X |
| Security Best Practices Away from the Office – 9:37 min | X | |
| Safe Internet Use – 6:09 min | X | X |
| Protecting the Workplace from Identity Fraud – 6:58 min | X | |
| Social Media Security – 11:02 min | X | |
| Device Management – Internet of Things – 7:25 min | X | X |
| Todays Risks – Acceptable Use of Electronic Resources – 7:46 min | X | X |
Are you ready to train your employees on the PCI DSS and how to protect your organization and customer data?
A Few Past Clients & Partners
 CFISA’s Security Awareness Training Level II course has been certified for employee training in Texas by the Texas Department of Information Resources since 2020.
CFISA’s Security Awareness Training Level II course has been certified for employee training in Texas by the Texas Department of Information Resources since 2020.
Subscription Pricing Benefits
A recurring subscription for security awareness training offers several advantages over the purchase of per-user seats with an expiration. The primary benefits being:
- Flexibility and Scalability:
- Pause at any time — easily reactivate to train new employees
- Cost-Efficiency — no long term contracts
- Continuous Learning — train and re-train as often as you need
- Better Employee Engagement
- Timely Updates
- Reduced Administrative Overhead
- And More…
The Center for Information Security Awareness (CFISA) provides online employee Cyber Security Awareness Courses including PCI DSS, HIPAA, InfragardAwareness and well as on-line webinars and on-site training.

 CEO and Founder Michael Levin is a former Secret Service Agent and Deputy Director of the National Cyber Security Division of the Department of Homeland Security. After retiring, Michael founded CFISA in 2007 to help businesses, academia, and government agencies teach their employees best practices to combat the onslaught of cybercrime.
CEO and Founder Michael Levin is a former Secret Service Agent and Deputy Director of the National Cyber Security Division of the Department of Homeland Security. After retiring, Michael founded CFISA in 2007 to help businesses, academia, and government agencies teach their employees best practices to combat the onslaught of cybercrime.
Michael has created engaging, affordable and compliant training. By personalizing these lessons Michael makes learning easy and effective. CFISA also makes it easy for customers to implement Michael’s courses by allowing them to run the training in their own learning management system (LMS). Alternatively, CFISA will host training for them.











